How is Technology transforming the Landscape of Long-term Care Facilities?

As per a report published by the forum ConsumerAffairs on long-term care status in the US; “Day-based care centers have approximately 286,000 individuals, assisted living facilities house around 811,500 residents, and nursing homes have 1,347,600 people staying on a long-term basis.”
“It has been predicted that the number of people receiving care in each of the aforementioned spaces will increase sharply in the coming years and this number may even become double by the end of the year 2030. Such a situation can pressurize the existing care network and accelerate care providing costs.”
To equip the long-term care network with added capabilities and reduced expenses, technology is the one-stop solution. Consequently, a technology-infused approach is gaining momentum in long-term care facilities. Modern technologies bring a lot to the table, not only for care facility owners but also for the patients and elderly individuals receiving care.
This post sheds light on the various technologies that are transforming the landscape of care facilities. A quick read will provide you with an idea of why investing in creating a technology-empowered infrastructure; will prove advantageous for your care facility in the long run.
What is a Long-term Care Facility?
Long-term care facilities offer medical as well as personal support to individuals who are no longer able to perform daily activities on their own, and hence are not in a position to live independently. Usually, long-term care is required by elderly individuals, patients suffering from chronic illnesses and related mobility problems, individuals battling mental instability issues, or persons who are unable to perform daily activities due to age-related or other impairments.
The entities offering such kind of care include nursing homes, CCRCs (Continuing Care Retirement Communities), SNFs (Skilled Nursing Facilities), and ALFs (Assisted Living Facilities). These facilities provide a safe and assisted environment to live in and offer the necessary care to residents.
Technology-powered Approach in Long-term Care Facilities: Benefits
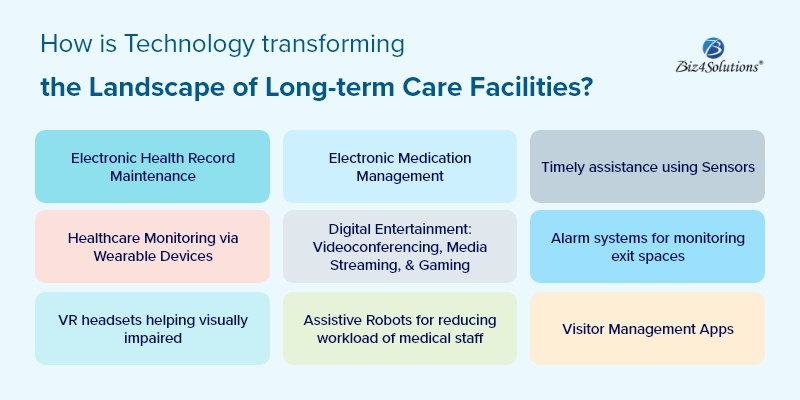
Electronic Health Record Maintenance/Sharing Systems
Electronic record systems improve the quality of care and enable care-providing centers to comply with standard regulations regarding healthcare data collection & auditing. Moreover, if data is codified, IT systems can be used to provide alerts to caregivers and allow care teams to make better and informed decisions. Furthermore, superior quality data can deliver robust, meaningful, and transparent reporting. And, flawless collection of data and accurate reporting improve administrative workflows for care-providing entities.
Electronic healthcare systems enable providers to offer customer-centric care and improve the transparency of their services. Electronic Health Record Systems like EHR and EMR collect and securely store the entire medical history of care facility residents. This information includes data on healthcare conditions, chronic diseases (if any), allergies, ongoing medications, etc. Also, the preferences mentioned by the care facility residents as well as their family members are recorded in such systems. This arrangement ensures that there are no chances of any misses or errors by the care providers.
The technology of electronic health records sharing with doctors, medical facilities, and other care-providing facilities, makes sure that no minor detail is missed during healthcare data transfer or transition phases.
Electronic Medication Management
One of the most tedious and time-consuming tasks for nurses and professional caregivers is managing medication passes manually. Moreover, the chances of grave errors are very high in manual medication management. And, if the wrong medication is administered to a resident, it leads to disastrous outcomes for the patient as well as the caregiver involved.
As such, care facilities these days are adopting eMAR (Electronic Medication Administration Records) systems to track medication adherence. eMARs are software systems that can be operated by care facility staff using tablets, laptops, or hand-held devices, while they are on rounds. These systems document the medications prescribed to every care facility resident and also how these medicines are passed to them by the caregiving staff. This has resulted in speedier and error-free medication passes. And, if these systems are integrated with pharmacy chains and GPS, residents have an added advantage during care facility transitions as well as hospital admissions during emergencies.
Automatic medication dispensers are meant for residents who can take medication on their own with slight assistance. Such software is programmed by the caregiver in a manner that individuals get timely medication alerts. In case, a resident misses any dosage, the software automatically locks that dose to prevent double dosing.
Timely assistance using Sensors
The power of sensors is being utilized in the healthcare sector and with time, sensors are getting smarter. Sensors are providing more flexibility to individuals availing of assisted living by allowing them to move freely without worry. Sensors send instant alerts during emergencies so that individuals receive timely assistance. Biosensors and activity sensors can be encapsulated within lifeline devices like pacemakers or placed within the care facility resident’s environment. These sensors work wonders in monitoring the overall health of an individual and identifying the wellness risks.
Take a look at some exceptional sensors designed by healthcare app developers. GPS Smart Sole in unison with T-Mobile employs satellite monitoring technology. Here, sensors are embedded inside the sole of individuals’ shoes for tracking their movement and exact location within the care facility. BAM Labs has coined a bed sensor mat that will track moisture, respiration rate, sleep patterns, etc. P&C Pharma had developed INSTA Compounding System that will transform pills into a liquid with a pleasant smell and taste. This technology is meant for persons who find it challenging to swallow pills.
Healthcare Monitoring via Wearable Devices
Wearable devices are excellent tools for remotely monitoring and alerting the care-providing staff about patients’ health vitals as well as their changing states of consciousness like motor activity, sleep patterns, etc. This helps in detecting any abnormalities or changes in health parameters that may be early symptoms of any disease or medical condition. Timely detection of health issues enables care providers to adopt preventive measures well in advance.
A common example of wearables used for patient care is smart watches and wristbands designed by brands like Fitbit. SmartSox, a wearable device meant for diabetic patient care, employs fiber optics technology for detecting excessive heat, pressure, and misplaced joint angles that can lead to foot ulcers in patients. MIT is in the process of crafting a smart shirt that will identify the commencement of a heart attack in individuals and also, administer CPR.
The mobile personal emergency system, commonly called mPERS is empowered to locate individuals’ current location, detect falls or accidents, and most importantly provide an SOS button. When that SOS button is pressed the device auto-dials a response team or family members to notify about the fall and ask for help. mPERS devices have a way superior battery life as compared to smartphones; these devices can last up to thirty days if put on sleep mode.
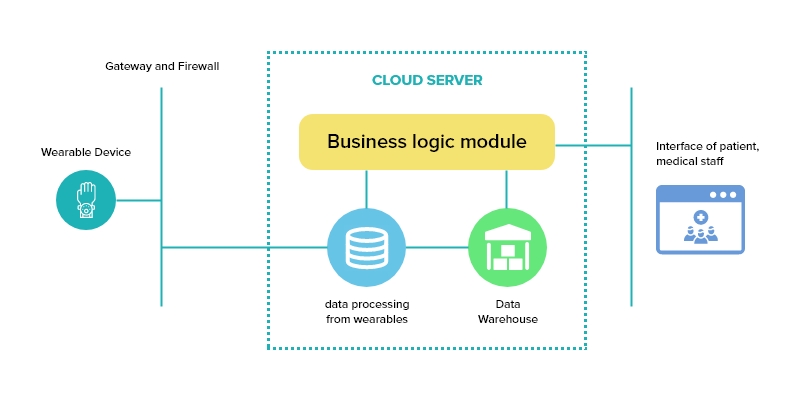
Here’s how a wearable healthcare device functions:
Intuitive Computing Technologies
Intuitive computing technologies like touchscreen electronic devices and graphic UIs prove advantageous for the staff as well as the residents of a long-term care facility. Using such amazing technologies, front-line caregivers can enter data using the feature of voice activation. This saves time and effort wasted in data entry tasks. Care facility residents can stay connected with friends and family through internet browsing, social networking, and e-mail exchanging; they can avail of memory-boosting activities as well.
Digital Entertainment: Videoconferencing, Media Streaming, & Gaming
Digital entertainment technologies elevate patient experiences to the next level. The videoconferencing technology help residents of a long-term care facility stay connected with family members and friends when frequent in-person visits are not possible. As a result, residents are able to interact with loved ones who stay in other locations, more frequently than ever before. Two-way videoconferencing contributes greatly to improving the mental health of residents. Residents can also leverage video conferencing for telemedicine doctor consultations in case of minor ailments.
Media streaming makes way for watching videos listening to music, and many more entertainment options for care home residents. Media channels can also be utilized for accessing newspaper content and gathering information about the outside world and other topics of interest.
Gaming for care facility residents? Yes, you got it right! Tech-savvy individuals residing in a care home can leverage the full potential of the gaming technology. Games, crossword puzzles, etc. are brain-stimulating as well as pleasurable activities that keep residents engaged and happy. And, by the next decade, the demand for digital entertainment in care facilities is expected to skyrocket.
Infrared/Radio Frequency
Elopement alarm systems powered by technologies like infrared & radio frequency can be paired with tracking systems for monitoring exit doorways, elevators, outdoor spaces, etc. Such technology will alarm the caregiving staff and help them locate any resident who has left the facility.
VR Headsets
The usage of Virtual Reality headsets in the realm of long-term patient care is a recent innovation. Its implementation will lead to exceptional outcomes for the residents of a long-term care facility. VR headsets can help vision-impaired individuals (like persons suffering from macular degeneration) to magnify/zoom in for viewing the world around them in a better way. Furthermore, VR can effectively manage the levels of pain and anxiety in elderly persons.
Assistive Robots (AT/AR)
Assistive robots (AT/AR) are a new approach that is set to transform the operations of a care facility. AT/AR promises to create a stimulating environment for the residents of a care facility and at the same time, reduce the workload for the staff engaged in providing care. Several LTCFs are in the process of implementing this innovative approach. AT/AR technology comes with offerings like service robots, screen readers, communication boards, positioning devices, etc. that are helpful for people with functional disabilities. Robots are employed for performing a wide range of tasks like providing assistance for fundamental needs, resolving logistical challenges, monitoring activities, ensuring security, and cleaning activities.
AT/AR technology not only facilitates assisted living but also reduces operational expenses resulting in lower healthcare costs for patients. This approach also minimizes the workload for professional caregivers and addresses the challenge of nursing staff shortage in long-term care facilities.
Visitor Management Apps
One of the commonest threats faced by the residents of long-term care facilities is the chances of disease-causing viruses entering the premises through visitors. Ever since the outbreak of the coronavirus pandemic, this aspect became a crucial challenge for any care facility.
Visitor management apps have been designed to address this issue. These apps follow a contactless visitor check-in process executed using smartphones and maintain the records of all visitors so that they can be easily contacted later if required. This approach can minimize the chances of disease transmission to a certain extent.
In a Nutshell:
The implementation of emerging technologies in long-term care facilities has made care services more affordable for residents and has smartened the workflow of care centers. A technology-powered approach has improved the quality and convenience quotient of delivering care, healthcare monitoring, medication adherence, and interaction between residents and caregivers. The benefits for residents owing to the usage of software apps, tools, and devices include increased mobility, more security, and a better quality lifestyle. More advanced technological innovations in the coming years will equip care homes with unimaginable capabilities.
Therefore, long-term care facilities should embrace a technological approach for staying competitive and fulfilling new-age consumer expectations. It’s advisable for care providers to seek professional assistance from experienced healthcare application development services for tailoring customized software as per the requirements of their care facility.



